Hackers have venetian eroticism vs high renaissance worksdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 9 Tech Products That Were Too Early to Market
9 Tech Products That Were Too Early to Market
 The Morning News Roundup of November 26, 2014
The Morning News Roundup of November 26, 2014
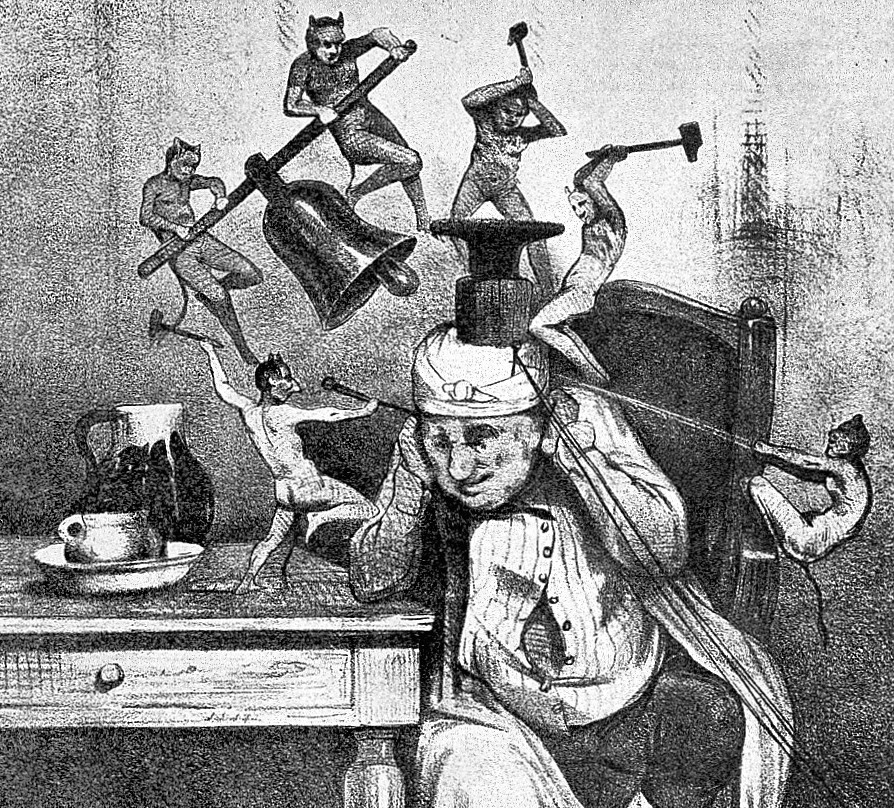 Why Migraines are the Most Glamorous of Headaches
Why Migraines are the Most Glamorous of Headaches
 'Top Boy' Season 5 review: The powerful end this masterpiece of a series deserves
'Top Boy' Season 5 review: The powerful end this masterpiece of a series deserves
 Celtic vs. Bayern Munich 2025 livestream: Watch Champions League for free
Celtic vs. Bayern Munich 2025 livestream: Watch Champions League for free
 Could the AI Drake and Weeknd song actually win a Grammy?
Could the AI Drake and Weeknd song actually win a Grammy?
 A Marvelous Crutch: An Interview with Brad Zellar
A Marvelous Crutch: An Interview with Brad Zellar
 The Urbane Turkey
The Urbane Turkey
 Best iPad deal: Save $70 on 10th Gen Apple iPad
Best iPad deal: Save $70 on 10th Gen Apple iPad
 Polestar's new electric car will have a smartphone to match
Polestar's new electric car will have a smartphone to match
 Trump's foreign aid freeze halts funding for digital diplomacy bureau
Trump's foreign aid freeze halts funding for digital diplomacy bureau
 Who Are These Future Rock
Who Are These Future Rock
 Wordle today: Here's the answer and hints for September 7
Wordle today: Here's the answer and hints for September 7
 The Morning News Roundup for November 21, 2014
The Morning News Roundup for November 21, 2014
 Trump praises storm response as historic disaster unfolds in Houston
Trump praises storm response as historic disaster unfolds in Houston
 Barry Gifford’s Novels Find a New Generation of Readers
Barry Gifford’s Novels Find a New Generation of Readers
 Pinterest unveils AI body type tech to increase representation
Pinterest unveils AI body type tech to increase representation
 The Morning News Roundup for November 28, 2014
The Morning News Roundup for November 28, 2014
 Ms. Frizzle spotted at Science Marches across the globe
Ms. Frizzle spotted at Science Marches across the globe
 Apple's Vision Pro will have iPad and iPhone apps from the start
Apple's Vision Pro will have iPad and iPhone apps from the start
Antonio Lobo Antunes on 'The Land at the End of the World' by Anderson TepperNearly 25,000 Twitter users pay to subscribe to Elon Musk's exclusive tweetsCalifornia Girls by Zan RomanoffAdaptation by Sadie SteinAge Gaps; Authorial Décor by Sadie SteinFacebook defends letting Trump spread misinformation on mailBeyoncé shares open letter calling for charges in Breonna Taylor caseWilliam Burroughs Catches Some Rays by Sadie SteinA Week in Culture: Tom Nissley, Writer and GameSnapchat's My AI is divisive among usersIt’s About to Get Really Girly by The Paris ReviewLarry David Humor; Fairies and Mushrooms by Sadie SteinMicrosoft removes Xbox gameplay video sharing to Twitter after API fee hikeWells Tower, DBC Pierre, and Tobias Wolff by Chris FlynnPaying for porn should be the postStaff Picks: Sea Voyages; Cats in Space by The Paris Review'Shadowbanned' tweets are now officially labeled on TwitterTexas Forever by Adam Wilson'Atlanta's Missing and Murdered: The Lost Children' HBO Doc: ReviewHere's how to *hypothetically* take down a racist statue with tips from an archaeologist The Women's Strike fizzled because Americans can't stop working Top 9 emojis if you're, like, really into graphs How NASA found India's long PSA: The new 'Beauty and the Beast' soundtrack is streaming on Spotify Winter to finally show up as blizzard looms from Philly to Boston The augmented reality headset wars have begun Sean Spicer channels Melissa McCarthy during a White House press conference Sorry, iPhone fans, the latest Snapchat Bitmoji feature is Android only The 'Trainspotting' sequel to hit U.S. at secret SXSW screening Automate Me: How to use Gmail templates to answer emails quicker Los Angeles' LGBTQ pride will be replaced by a protest march Republican bill would let employers demand workers’ get genetic testing Hurricane forecasters sent a blunt warning to their bosses Bert and Robert Rodriguez crash 'The Mashable Show' at SXSW New fund puts $141 million toward digital finance in the developing world One perfume wants to be the next weapon against cybersecurity attacks GM will push the future of cars, with or without Trump's help Watch Scarlett Johansson skewer Ivanka Trump in 'SNL' perfume ad India extends paid maternity leave to 26 weeks, citizens hail the move There's now a 'She persisted' energy bar because this is what we've come to
1.5716s , 10195.078125 kb
Copyright © 2025 Powered by 【venetian eroticism vs high renaissance works】,Information Information Network