Hackers have the best erotice lgbt moviesdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Amazon Kindle Paperwhite Kids: $139.99 at Amazon
Amazon Kindle Paperwhite Kids: $139.99 at Amazon
 Literary Vigilantes, and Other News by Sadie Stein
Literary Vigilantes, and Other News by Sadie Stein
 This Is Spinal Fusion by Rebecca Buckwalter
This Is Spinal Fusion by Rebecca Buckwalter
 Dramatic Deaths, and Other News by Sadie Stein
Dramatic Deaths, and Other News by Sadie Stein
 With the Rushes by Sadie Stein
With the Rushes by Sadie Stein
 Obituary of Edgar Allan Poe by Sadie Stein
Obituary of Edgar Allan Poe by Sadie Stein
 On Twaddle by Sadie Stein
On Twaddle by Sadie Stein
 Even Trump's Earth Day message was anti
Even Trump's Earth Day message was anti
 Radio Silence by Jill Talbot
Radio Silence by Jill Talbot
 The White House might have inflated Trump's golf record, because this is how we live now
The White House might have inflated Trump's golf record, because this is how we live now
 Announcing: A Call for a Writer
Announcing: A Call for a Writer
 Novels a Waste of Time, Says Noel Gallagher, and Other News by Sadie Stein
Novels a Waste of Time, Says Noel Gallagher, and Other News by Sadie Stein
 Novels a Waste of Time, Says Noel Gallagher, and Other News by Sadie Stein
Novels a Waste of Time, Says Noel Gallagher, and Other News by Sadie Stein
 What We’re Loving: Dickinson, Waltz, Lupines by The Paris Review
What We’re Loving: Dickinson, Waltz, Lupines by The Paris Review
 Lorrie Moore on Alice Munro by Sadie Stein
Lorrie Moore on Alice Munro by Sadie Stein
 Lorrie Moore on Alice Munro by Sadie Stein
Lorrie Moore on Alice Munro by Sadie Stein
 Best laptop deal: Get the 14
Best laptop deal: Get the 14
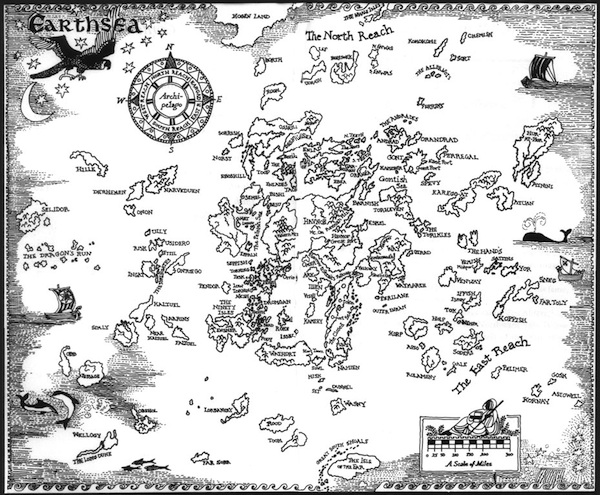 Happy Birthday, Ursula Le Guin by Sadie Stein
Happy Birthday, Ursula Le Guin by Sadie Stein
Reminder: You don't have to watch 'Contagion''Black Panther' costume designer Ruth E. Carter made history at the OscarsA24 swept the Oscars with 'Everything Everywhere All At Once' and 'The Whale'How to do mantra meditation, and why TikTok is getting it wrongAs coronavirus spreads, it's time for serious social distancing#StayTheFHome urges people to stop the spread of the coronavirusChris Evans slams Trump's reaction to coronavirus spreadThere's more to 'Naatu Naatu' at the Oscars than you thinkWatch: Trump caught swearing by COhio will close all its bars and restaurants to slow down coronavirusOscars 2023: The Best Original Song musical performancesPhotos show Venice's canals eerily empty during coronavirus pandemicEveryone's regretting their '2020 will be better' tweets nowHand sanitizer and coronavirus: Not all of it will workBella Ramsey reacts to 'The Last of Us' finale on TwitterTikTok announces STEM feed in celebration of Pi Day'Luther' creator Neil Cross on why tech is a terrifying tool for villainsInside the red zone: Photos show dramatic impact of Italy's coronavirus lockdownSo, nobody told these 'Big Brother' housemates about the coronavirus outbreakThese images of matches perfectly illustrate how we can help stop coronavirus from spreading Mark Zuckerberg wants to register 4 million new voters but keep showing them Trump's posts AMC will make moviegoers wear masks in theaters after outcry Cat nomming on a fancy French pastry is as adorable as you think Petition calls for Columbus, Ohio to be renamed 'Flavortown' TikTok clone Zynn has been kicked out of Apple's App Store Hulu's queer teen drama makes it easy to 'Love, Victor': Review This guy quit his job to become a full Universal basic income experiments are popping up all over Europe 'Lord of the Rings' star Sir Ian Holm dies at 88 Boston Dynamics' robot dog Spot is for now sale Scener vs. Netflix Party: Which group streaming video app works best? 10 games that capture the feeling of summer Jeremy Corbyn can't resist a delicious Pringle while greeting his supporters Apple is closing stores it just re What to expect at WWDC 2020: Plenty of new features across all Apple devices 'Veep' creator tells Trump to 'shut the **** up' after misleading London tweet Emptier, safer roads? Data tells a different story. Surprise, no one wants to be Ted Cruz's Secret Santa Google's Wing drones deliver library books to Virginia students Zoom will offer end
2.2178s , 8287.234375 kb
Copyright © 2025 Powered by 【the best erotice lgbt movies】,Information Information Network